Archive
Configuring Forefront Threat Management Gateway (TMG) URL Filtering to Fail Closed
The URL filtering feature in Microsoft Forefront Threat Management Gateway (TMG) 2010 leverages the Microsoft Reputation Services (MRS) for URL categorization. MRS is a cloud-based, multi-vendor URL database that is supplemented by intelligence gathered from various Microsoft online service offerings, telemetry from TMG, and direct user feedback. At a high level, when a request is made for a public URL, the firewall service will contact MRS to determine which category or categories the URL belongs to. TMG then compares this against the configured firewall policy to determine if the request is allowed or denied (this categorization is cached locally, so subsequent requests for the same URL do not require another trip to the cloud).
What happens if TMG cannot contact the MRS services to categorize a URL? By default, if TMG does not receive a reply from MRS the URL is categorized as Unknown and an alert is raised. In essence, the fail open or fail closed policy can be determined by either allowing or denying the category unknown. Allow the unknown category to fail open, or deny it to fail closed.
Of course there are some implications to denying the unknown category. There may be legitimate sites that users visit that are not yet categorized by MRS. Although you could manually categorize these URLs in the TMG management console, doing so would be a tedious and time consuming process. Blocking access to unknown sites until an administrator could categorize them manually would also be intrusive and disruptive, and a potential productivity killer.
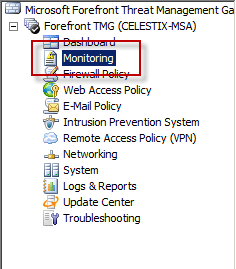
A better solution to enable a fail closed policy would be to configure the URL Categorization Server Unavailable alert to stop the TMG firewall service when triggered. To do this, open the TMG management console and highlight the monitoring node in the navigation tree.
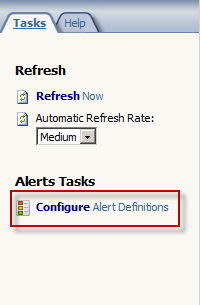
Select the alerts tab and in the tasks pane click the Configure Alert Definitions link.
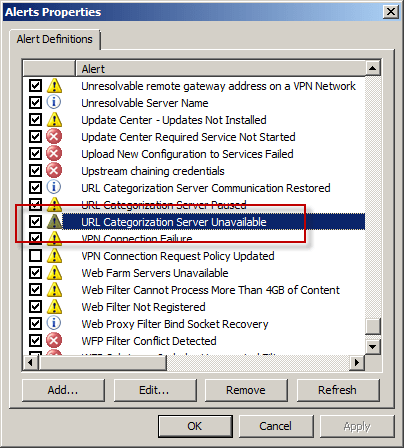
Highlight the URL Categorization Server Unavailable alert and choose Edit…
Select the Actions tab, and then check the Stop selected services option and choose Select…
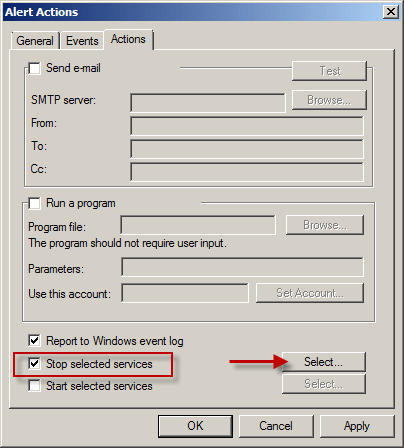
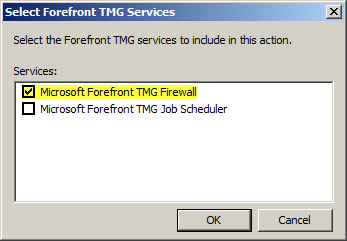
Select Microsoft Forefront TMG Firewall.
For Enterprise arrays, consider creating separate alerts for each array member. In the event a single array member is unable to contact MRS, only that firewall will stop processing traffic. To do this, select the Events tab and select an array member from the By server: dropdown box.
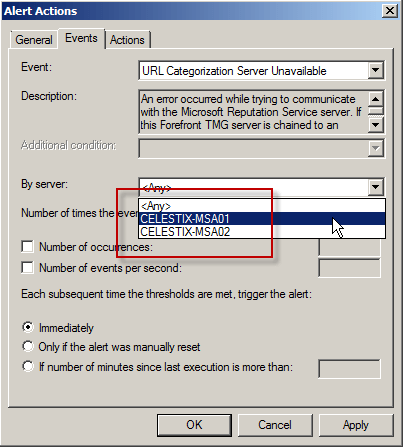
Note: To avoid interrupting service due to temporary unavailability of MRS, you may want to configure the alert to be triggered after a certain number of occurrences, and perhaps specify the number of minutes since the last execution of the event occurred.
Once complete, create an identical alert for each of the remaining array members. You can do this by choosing clicking the Configure Alert Definitions link and selecting Add…, then follow the New Alert Configuration Wizard.
TechNet Edge Interview – TMG and UAG Deployment Options
Recently I had the pleasure of sitting down with David Tesar from TechNet Edge to discuss deployment options for TMG and UAG. I had the opportunity to talk about some of the potential pitfalls to deploying TMG and UAG on a virtual infrastructure, specifically relating to security and performance. You can watch the video here. Enjoy!
Creating User Mode Process Dumps in Microsoft Forefront Threat Management Gateway (TMG) 2010
In a recent post on his blog, Yuri Diogenes shared with us how to create a manual dump of the wspsrv.exe process in TMG by using the Windows Task Manager. This is tremendously helpful in many situations, but there are scenarios that require more flexibility. For this I use procdump.exe from Sysinternals. To create a dump of a user mode process, enter the following command:
procdump <process>
For example, creating a dump of the wspsrv.exe process would look like this:
procdump wspsrv
This will immediately generate a dump file called wspsrv.dmp.
Procdump provides additional flexibility by allowing you to trigger a dump based on specific thresholds. This is extremely useful when troubleshooting intermittent high CPU utilization issues with TMG. For example, if you wanted to create a dump of the wspsrv.exe process when CPU utilization reaches 90% for more than 5 seconds, enter the following command:
procdump –c 90 –s 5 c:\wspsrv.dmp
When CPU utilization stays at or above 90% for more than 5 seconds, a user mode process dump will be generated and saved in the file c:\wspsrv.dmp. This can be beneficial in situations where high CPU utilization prevents you from using the mouse or typing commands at the command prompt. Automating the task of capturing dumps based on triggers also frees the administrator from having to be at the console when the symptom occurs. Additional command line switches allow you to create multiple dumps, increasing your chances of collecting accurate data for troubleshooting.





