Archive
Publish DirectAccess with Forefront TMG 2010
DirectAccess is a compelling remote access solution that provides seamless and transparent, always-on, bi-directional remote corporate network connectivity for managed Windows clients. In Windows Server 2008 R2 and Forefront Unified Access Gateway (UAG) 2010, the DirectAccess server had to be configured with two network adapters, with the external network interface configured with two consecutive public IPv4 addresses. Many security engineers were understandably concerned about exposing a domain-joined Windows server directly to the public Internet, which limited the adoption of the technology. Beginning with Windows Server 2012, DirectAccess is integrated in to the operating system and provides more flexible network configuration. DirectAccess can now be deployed behind an existing edge security solution performing NAT, and even supports single-NIC configuration.
The Forefront TMG 2010 firewall is an excellent choice to provide essential protection for the DirectAccess workload. When DirectAccess is deployed behind a NAT device, the only firewall port that needs to be opened is TCP port 443 (HTTPS).
When publishing DirectAccess with TMG, it is important to use a server publishing rule and not a web publishing rule. To publish DirectAccess, open the Forefront TMG 2010 management console, right-click Firewall Policy in the navigation tree, and then choose New Non-Web Server Publishing Rule.

Provide a descriptive name for the rule, enter the IP address of the DirectAccess server, choose HTTPS Server for the protocol, and then select the network interface on which to listen for these requests.

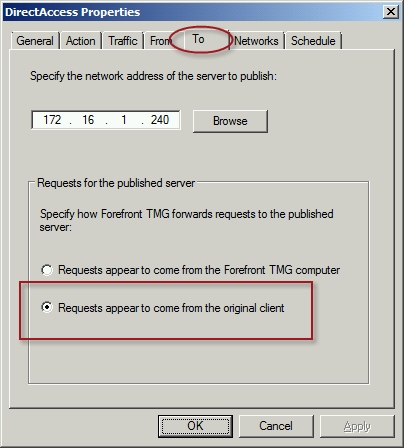
To ensure the proper operation of Receive Side Scaling (RSS) on the DirectAccess server, it is recommended that the server be configured to use TMG as its default gateway and to configure the publishing rule on TMG using the option Requests appear to come from the original client.
Also, TMG does not support load balancing for server publishing rules, so it is not possible to deliver traffic to multiple back end servers using TMG. For high availability and to provide for scalability, it is recommended to configure load balancing for DirectAccess using NLB or an external load balancer (recommended) and publish the virtual IP address (VIP) using the steps described above.
To learn more about DirectAccess, visit http://directaccess.richardhicks.com/
Enable TLS Forward Secrecy for Forefront TMG 2010 Published Web Sites
Last year I wrote an article for ISAserver.org that outlined in detail how to improve SSL and TLS security for web sites published using Forefront TMG 2010. In its default configuration, Windows Server 2008 R2 and Forefront TMG leave quite a bit to be desired in terms of SSL and TLS security. In the article I demonstrated how to dramatically improve the security posture of TMG when publishing web sites that use SSL and TLS. At the time I wrote the article it was not recommended to enable forward secrecy, so the changes I originally proposed resulted in an “A” score from the Qualys SSL Labs test site. However, times have changed since then, and with the recent revelations of wide spread government spying, it is now recommended to enable forward secrecy by default. Sites that don’t support forward secrecy will now receive a reduced grade.

To accomplish this on the Forefront TMG 2010 firewall, open the Local Group Policy Editor (gpedit.msc) and navigate to Computer Configuration, Administrative Templates, Network, SSL Configuration Settings. Double-click SSL Cipher Suite Order and choose Enabled. Copy the list of SSL cipher suites to a blank notepad document and then move all of the cipher suites that begin with TLS_ECDHE_RSA_WITH_AES_ to the front of the list. Use caution here because the list cannot have any extra commas, line breaks, or spaces at all. Paste the updated list back in to the SSL Cipher Suites box and click Ok.

The server will have to be restarted for the changes to take effect. Once complete, forward secrecy will now be used by modern browsers and you should once again receive an “A” grade from SSL Labs.

Publishing Exchange 2013 Outlook Web App with Forefront TMG 2010
Recently I wrote an article for ISAserver.org about publishing Exchange 2013 Outlook Web App (OWA) using Forefront TMG 2010. In spite of the fact that many organizations are migrating their e-mail services to the cloud, there are many organizations who cannot, for a variety of reasons, take advantage of cloud services for e-mail. This makes Exchange 2013 a compelling upgrade for many companies. Historically Forefront TMG 2010 and its predecessors were the go-to service for securing access to on-premises Exchange implementations. Forefront TMG 2010 supports OWA publishing with native publishing wizards, allowing you to select which version of Exchange you are publishing, with the added bonus of providing in-box forms-based authentication (FBA) templates that matched the look and feel of the Exchange version you were publishing. Since Forefront TMG 2010 has been deprecated, Microsoft has not updated Forefront TMG 2010 to include support for Exchange 2013 OWA. However, you can still publish Exchange 2013 OWA using Forefront TMG by following the instructions outlined in my ISAserver.org post. When using this method, the Exchange 2010 FBA templates are used. This makes the user experience somewhat disjointed, with the FBA pages not matching the new, updated look and feel of OWA 2013. To remedy this, I reached out to my good friend Scott Glew at Fastvue. Scott is a terrific web developer, as evidenced by the amazing UI included with the TMG Reporter solution. In short order, Scott whipped up some customized Forefront TMG 2010 FBA templates to match the look and feel of OWA 2013 and has made them available for free. Now if you’re publishing Exchange 2013 OWA using Forefront TMG 2010, you can download these custom templates and use them to provide a consistent experience for your Exchange OWA users. Enjoy!
Forefront UAG 2010 Video Training Course Now Available
I’m happy to announce that my latest Trainsignal video training course is now available! This new video training course is on Forefront Unified Access Gateway (UAG) 2010. It is an introductory course on Forefront UAG designed to teach network engineers and security administrators the basic essentials of planning, preparing, installing, configuring, monitoring, and maintain a Forefront UAG 2010 remote access solution. In the course I demonstrate how to publish popular Microsoft on-premises applications like SharePoint and Exchange Outlook Web App (OWA). In addition I cover publishing Remote Desktop Services and VPN remote access. I also provide a high level explanation of endpoint detection and endpoint policy enforcement and demonstrate how to provide high availability for the solution. Here is the entire course outline:
Lesson 1 – Introduction and Course Outline
Lesson 2 – Forefront UAG 2010 Overview
Lesson 3 – Planning to Deploy Forefront UAG 2010
Lesson 4 – Installing and Configuring Forefront UAG 2010
Lesson 5 – Configuring a Portal
Lesson 6 – Publishing Exchange Outlook Web App
Lesson 7 – Publishing SharePoint
Lesson 8 – Publishing Remote Desktop Services
Lesson 9 – Configuring VPN Remote Access
Lesson 10 – Enabling Endpoint Detection
Lesson 11 – Configuring High Availability
Lesson 12 – Web Monitor Overview
Lesson 13 – Forefront UAG Backups
Once again I had the opportunity to work with my good friend and fellow Microsoft MVP Jordan Krause on this course. As he did in my previous Trainsignal video training course on Windows Server 2012 DirectAccess, Jordan served as the technical reviewer and provided valuable insight that ultimately made the course better. If you’re planning to implement Forefront UAG 2010 to provide secure remote access to both managed and non-managed systems and devices, be sure to sign up for a subscription at Trainsignal.com today! Not only will you have access to this video training course on Forefront UAG 2010, you will gain access to the entire Trainsignal library of content, including my course on Windows Server 2012 DirectAccess, all for just $49.00 per month!
Mastering Microsoft Forefront UAG 2010 Customization
Recently my good friends Ben (Erez) Ben-Ari and Rainier Amara announced their new book Mastering Microsoft Forefront UAG 2010 Customization, which is scheduled for release early next year. As many of you know, Ben is the author of the Microsoft Forefront UAG 2010 Administrator’s Handbook, an essential reference for anyone working with Forefront UAG 2010. The new book focuses on customization, which is one of the features that make Forefront UAG 2010 a powerful and compelling remote access solution. I have the tremendous privilege of serving as the book’s technical reviewer, and as I am getting an advanced look at Ben and Rainier’s work I can tell you this book will be a must-have for anyone working with Forefront UAG 2010. The book will be available in print and e-book formats and can be pre-ordered here.