Archive
Enable Authentication for SafeSearch Enforcement Rule in Forefront TMG 2010
SafeSearch enforcement in Forefront TMG 2010 is a simple and effective way to prevent users on your network from accessing explicit adult content via popular search engines. Enabling SafeSearch enforcement is accomplished by opening the Forefront TMG 2010 management console, highlighting the Web Access Policy node in the navigation tree, clicking the Configure SafeSearch link in the Tasks pane and selecting the option to Enable SafeSearch.
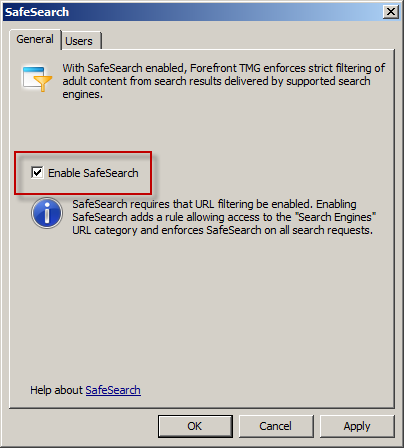
When SafeSearch is enabled a rule is created that grants access to all users from the Internal network to all sites in the Search Engines category.
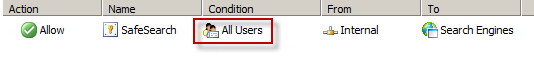
Effectively this grants unauthenticated access to many search engines including Bing, Google, and Yahoo. This level of access is quite broad and enables anonymous users to access quite a bit of content, which might not be desirable in some environments. It is not possible to change the users in the GUI either, unfortunately. However, it can be changed programmatically using COM and VBscript. For example, the following code will change the users from All Users to All Authenticated Users.
Dim Root, Array, Rule
Set Root = CreateObject("FPC.Root")
Set Array = Root.GetContainingArray()
Set Rule = Array.ArrayPolicy.PolicyRules("SafeSearch")
Rule.AccessProperties.UserSets.Add "All Authenticated Users", fpcInclude
Rule.AccessProperties.UserSets.RemoveSpecified "All Users"
Array.Save
Array.WaitForReload
Important Note: This change is not officially supported by Microsoft. If you make this change it may potentially cause other issues, so please proceed with caution.
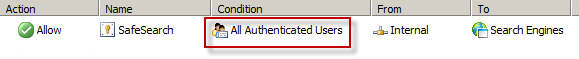
Once the script has completed the SafeSearch rule will now apply to All Authenticated Users and prevent unwanted anonymous access to web sites categorized as Search Engines.
Disable Logging on System Policy Rules in Forefront TMG 2010
I’ve written a number of articles on improving system performance and logging optimization over the years. As I’ve mentioned previously, this involves the security administrator reviewing each access rule and deciding if the traffic is interesting enough to require logging. If it is not, to improve performance and reduce log pollution it is advisable to disable logging for the access rule in question.
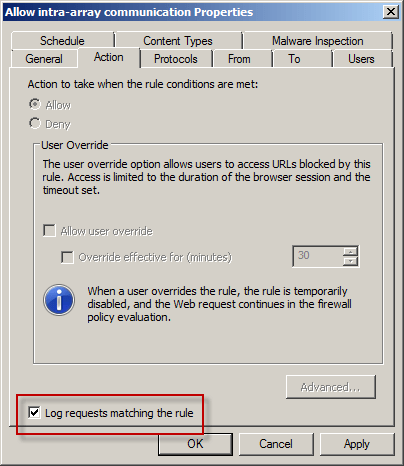
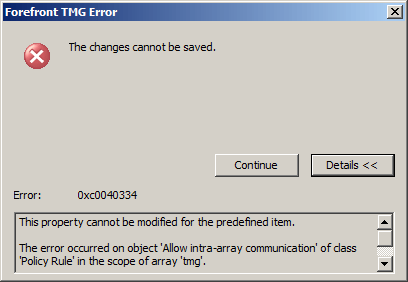
However, when attempting to make this change to a system policy rule you will encounter the following error:
The changes cannot be saved. Error: 0xc0040334 This property cannot be modified for the predefined item. The error occurred on object <policy rule name> of class ‘Policy Rule’ in the scope of array .
Unfortunately the system policy editor provides no facility to make this change in the GUI. To work around this limitation you can use COM to disable logging on system policy rules programmatically using the following script. In this example I’ve chosen to disable logging on the Allow intra-array communication system policy rule.
Option Explicit
Dim Root, Array, Rule
Set Root = CreateObject("FPC.Root")
Set Array = Root.GetContainingArray()
Set Rule = Array.SystemPolicy.PolicyRules.Item("Allow intra-array communication")
Rule.EnableLogging = False
Rule.Save
WScript.Echo “Done!”
Set Rule = Nothing
Set Array = Nothing
Set Root = Nothing
Note: To see this change reflected in the management console, hit F5 to refresh or close and reopen the console.
If you wish to disable logging for all system policy rules, alter the script to use a For Each Next construct as follows:
Set Rules = Array.SystemPolicy.PolicyRules For Each Rule in Rules Rule.EnableLogging = False Next
Configuring Forefront TMG 2010 HTTPS Inspection Inclusion List
When HTTPS inspection is configured and enabled on a Forefront TMG 2010 firewall, the administrator has the option to define web sites to exclude from HTTPS inspection. This may be required for a variety of reasons. For example, an administrator may need to exclude certain destinations to address privacy concerns, or perhaps HTTPS inspection breaks an application that uses SSL to tunnel non-HTTP protocols. All HTTPS web sites are inspected except for those sites defined as Destination Exceptions.

Beginning with Service Pack 2 (SP2) for Forefront TMG 2010, administrators can now define an explicit inclusion list for HTTPS inspection. Sites included on this list will be subject to HTTPS inspection, while all other destinations will be excluded. To define an HTTPS inspection inclusion list, create a Domain Name Set and populate it with those destinations for which you explicitly want to enforce HTTPS inspection.

After saving and applying the configuration, copy this VBScript file to the TMG firewall, then open an elevated command prompt and type the following command:
cscript.exe ConfigureHTTPSiInclusionList.vbs <DomainNameSetName>
Substitute <DomainNameSetName> in the command above with the name of the Domain Name Set created earlier. Once configured, the Destination Exceptions tab of the HTTPS Outbound Inspection properties will be greyed out, and only those sites included in the Domain Name Set defined as the HTTPS inspection inclusion list will be subject to HTTPS inspection. All other destinations will be excluded. You can still define Source Exceptions as needed, however.

Only one Domain Name Set can be specified as the HTTPS inspection inclusion list. Running the command without parameters removes any configured inclusion list and returns HTTPS inspection back to its original state.
For more information regarding HTTPS inspection inclusion lists, refer to KB2619986.




