Archive
Forefront TMG 2010 Configuration Error Alert
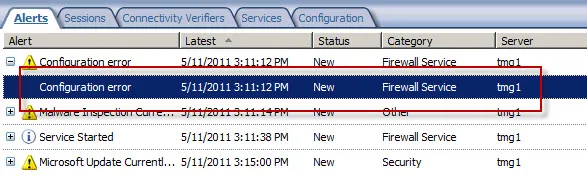
On a Forefront Threat Management Gateway (TMG) 2010 firewall you may encounter a Configuration Error alert like this:
The alert description states:
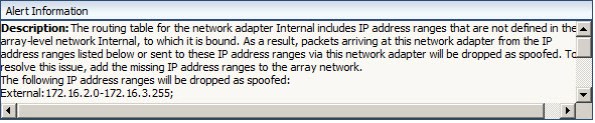
“The routing table for the network adapter Internal includes IP address ranges that are not defined in the array-level network Internal, to which it is bound. As a result, packets arriving at this network adapter from the IP address ranges listed below or sent to these IP address ranges via this network adapter will be dropped as spoofed. To resolve this issue, add the missing IP address ranges to the array network.
The following IP address ranges will be dropped as spoofed:
External:172.16.2.0-172.16.3.255;
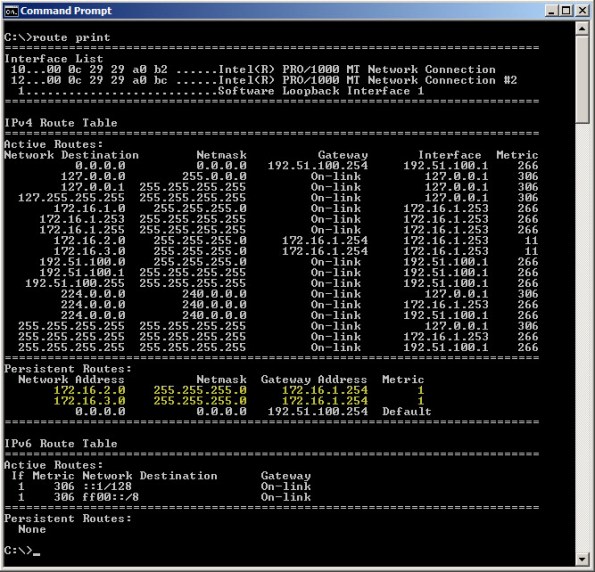
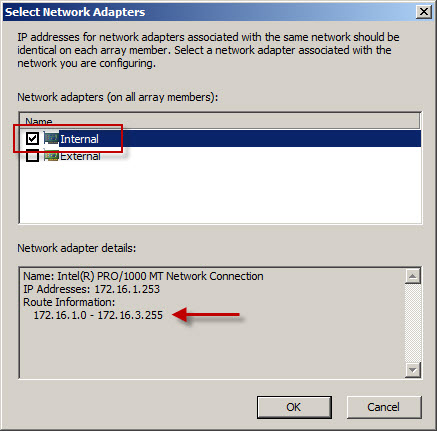
This alert is the result of the Forefront TMG firewall’s routing table and network definition being out of sync with each other. In this example, the routing table looks like this:
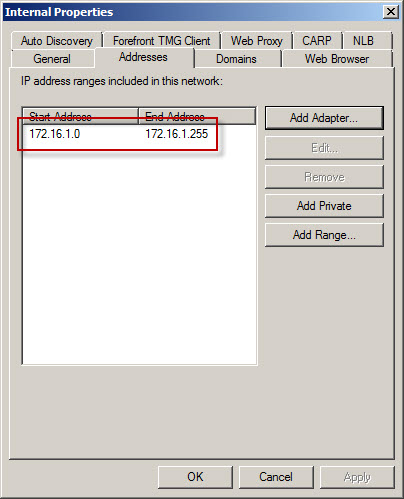
However, the Forefront TMG Internal network definition looks like this:
As you can see, the Forefront TMG firewall is configured with an Internal network IP address range of 172.16.1.0/24. However, the routing table contains additional static routes that also make the 172.16.2.0/24 and 172.16.3.0/24 networks reachable.
To resolve this issue, highlight the Networking node in the navigation tree, select the Networks tab in the center window, then highlight the network that corresponds to the IP address range contained in the alert. In our example the address range 172.16.2.0-172.16.3.255 also belongs to the Internal network. Right-click the Internal network and choose properties, choose the Addresses tab, then remove all address ranges previously configured. Next, choose Add Adapter and choose the network adapter for this network.
Using this method the IP address range for this network is built using the routing table for the network interface. This is the preferred method for defining IP address ranges for Forefront TMG networks. Save the changes and apply the configuration.
For more information on configuring network interfaces for Forefront TMG 2010 firewalls, please refer to Jason Jones’ excellent documentation on the subject here:
Recommended Network Adapter Configuration for Forefront TMG Standard Edition Servers
Recommended Network Adapter Configuration for Forefront TMG Enterprise Edition Servers
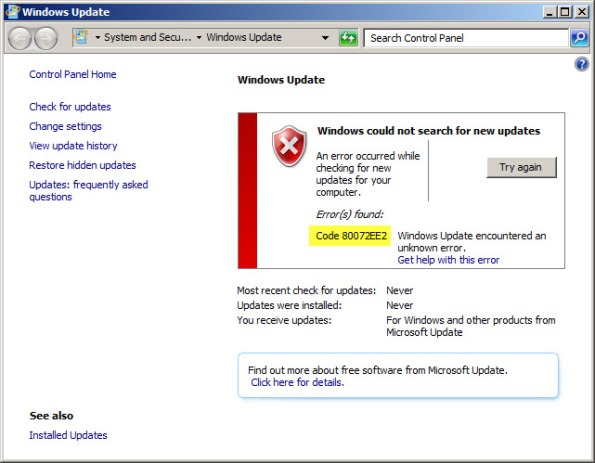
Running Windows Update on a TMG Firewall Fails with Result Code 80072EE2
Recently I have encountered a few instances in which the Windows Update client on a system with Forefront Threat Management Gateway (TMG) 2010 installed is unable to retrieve updates and fails with an error code of 80072EE2.
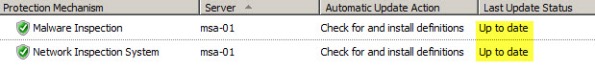
When this occurs, Malware Inspection and Network Inspection Systems signature updates are received without issue.
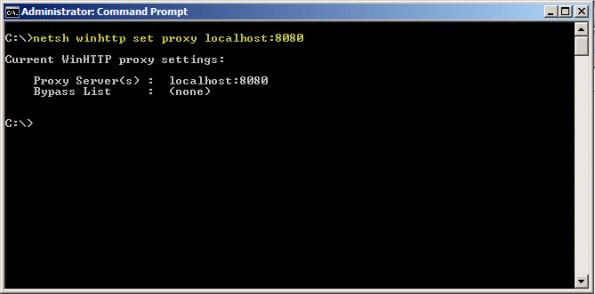
To resolve this issue, open an elevated command prompt and enter the following command:
netsh winhttp set proxy localhost:8080
If it is necessary to access HTTP and/or HTTPS web sites or services on your Internal network from the TMG firewall, you will need to configure the proxy bypass list. To learn how, enter the following command:
netsh winhttp set proxy ?
If you need to configure Windows Update on the TMG firewall to work with WSUS, read this blog post on the Forefront TMG product team blog.
Update for Microsoft ISA Server 2006 Standard with MS09-012
As many of you know, Microsoft security update MS09-012 can cause issues when installed on a Microsoft ISA firewall. These issues are related specifically to ISA 2004 and 2006 Standard Edition only, and only when it is installed on a system that has more than four processor cores. A workaround was originally posted by Jim Harrison on the ISA Product Team blog soon after the update was released. According to Jim, an update to address this issue is now available for ISA Server 2006. The update for ISA Server 2004 is still in the works. If you originally employed this workaround you are encouraged to install this new update.
It Starts…
After many years of consuming blog information from a variety of different sources, I have finally decided to become a contributor by creating this blog. My plan is to share with you some of the knowledge and experience I have gathered in working with Microsoft ISA Server for over ten years (dating back to Proxy 2.0!). I am currently employed by Celestix Networks as a Senior Sales Engineer, specializing in the MSA security appliance featuring Microsoft ISA Server 2006. I will endeavor to share with you relative, pertinent information that you will hopefully find useful. One of my mottos is “you can’t fix something if you don’t know how it works correctly in the first place”, so in support of that you will likely find references to information that I consider to be fundamental. A strong, foundational knowledge of any complex system is essential to any troubleshooting that takes place, and that is especially true in the world of enterprise networking.