Forefront Threat Management Gateway (TMG) and Windows Server 2008 Networking Scalability Features
Several years ago, Microsoft released the Scalable Networking Pack (SNP) for Windows Server 2003 SP1. The SNP included enhancements to the operating system’s networking stack to improve scalability and increase performance. Later the SNP features were included in Windows Server 2003 SP2. Veteran ISA firewall administrators will recall that the SNP adversely affected the operation of ISA, particularly when Network Load Balancing (NLB) was enabled. Since these features were enabled by default, disabling them after installing the SNP or Windows Server 2003 SP2 on an ISA firewall was a requirement. This was accomplished by modifying registry keys or installing a hotfix that disabled the SNP features.
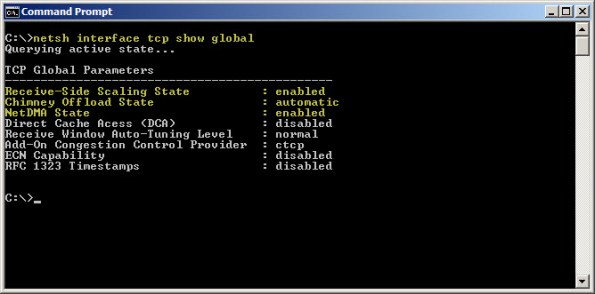
Today, the networking stack in Windows Server 2008 and Windows Server 2008 R2 both include the capabilities originally introduced with the SNP. Instead of modifying registry keys to enable/disable those features as we did in Windows Server 2003, they are now managed using netsh.exe. To view these parameters, enter the following command:
netsh interface tcp show global
As you can see, SNP components such as receive-side scaling, chimney offload, and NetDMA are enabled by default. Thankfully TMG is now fully compatible with all of the scalable networking features. There is no need to disable them unless you have a specific requirement to do so.





Useful; I did wonder about that!
“TMG is now fully compatible with all of the scalable networking features” .. hhmmmm not really i think
My TMG just failed not allowing any L2TP VPN connections to my server – the solution was to set DisableTaskOffload=1 which to my knowledge has something to do with the SNP.
My server used fully updated Broadcom nics!
So when it comes to Networking Scalability Features and Exchange/ISA/TMG – be afraid – be very afraid!
The problem you are experiencing is not related to SNP features, but rather to the Broadcom NIC. Broadcom interfaces have been known to cause many issues for ISA and TMG, especially the onboard interfaces in many industry standard servers. Here is an example of one documented issue with the RRAS service (which ISA/TMG depends on for VPN services) failing when using an onboard Broadcom interface.
Oh yes – those dreadfull Broadscum nics – since 2003 SP2 came out they have been nothing but trouble! I have used Intel nics since then but for the TMG i decided to give Broadscum a try again – big mistake.
Which TMG features are affected when using Broadcom NICs?
Many different firewall operations are affected by issues with Broadcom NICs. They occur most frequently with NLB and VPN, but I have seen issues with performance and throughput that have been related to them as well.
Is there any known workaround that could be implemented?
The only workaround I am aware of involves replacing Broadcom NICs with Intel NICs.
Hi all,
First of all, Richard, thank you for your fantastic blog !
Now, about these Broadcom NIC’s, we have 2 IBM Bladecenter servers with Broadcom 5709S.
I have disabled SNP features with netsh commands and still we have connectivity loss.
Can anybody help ?
Thank you in advance,
Mauro Rita
Thanks for the kind words, Mauro! As for your connectivity issues, all I can suggest is that you update to the latest drivers and see if that resolves the issue. If the issues persist, you may need to deploy TMG on a system that uses (or you can install) another brand of NIC.