Archive
Fastvue TMG Reporter v2.1 Now Available
Today Fastvue announced the general availability of TMG Reporter v2.1, the latest release of their advanced reporting and alerting platform built specifically for Forefront TMG 2010. I’ve been working with some of the early release builds and although this is technically considered a minor release, this latest update includes some important new features that make this a worthwhile and compelling upgrade. Here are some of the great new features included with TMG Reporter v2.1:
Activity Reports – Easily the single most important feature included in Fastvue TMG Reporter v2.1 is the addition of detailed activity reports. Prior to v2.1 only overview reports were available. You can now create extremely granular reports on user, site, category, or application activity that include timestamps, full URLs, browse time, category, and disposition (allowed or denied).
Scheduled Custom Reports – Another excellent new feature in Fastvue TMG Reporter v2.1 allows the administrator to create custom reports using the new filtering interface and schedule them for automated delivery to recipients.
Comprehensive Filtering – Fastvue TMG Reporter v2.1 includes a powerful new filtering facility that allows security administrator to dig deep in to the logging data to find the pertinent information they desire. The new enhanced filtering feature is available for use on all reports.
Drilldown Reporting – Another feature that has been greatly improved in the v2.1 release is drilldown reporting. Previously executing a drilldown report resulted in the creation of a completely new and separate report. With v2.1, the new drilldown report now respects the initial filter settings, allowing the administrator to see detailed information as necessary while maintaining the context that the original report was created within.
SQL Server integration – This is one of my favorite (and most requested!) new features. TMG Reporter v2.1 now includes native support for SQL server logging. There are many compelling reasons to configure the Forefront TMG 2010 firewall to log to an external SQL server, and now TMG Reporter can connect directly to your TMG firewall’s configured SQL server to collect report data.
Full support for Windows 8 and Server 2012 – You can now install TMG Reporter on Windows 8 and Windows Server 2012! This is great news as many organizations are beginning to deploy Windows 2012 server and Windows 8 desktops. The TMG Reporter installer now detects which server platform you are installing on and installs the necessary prerequisites automatically. The TMG Reporter web interface is also fully supported on Windows 8 with Internet Explorer 10 (modern and desktop).
Since its initial release a few years ago, Fastvue TMG Reporter has continued to add features and functionality. If you’re running an older version, or if you haven’t yet made the switch to TMG Reporter, the new capabilities in TMG Reporter v2.1 may finally compel you to take the leap and implement or upgrade to TMG Reporter v2.1 for your Forefront TMG monitoring, alerting, and report needs. Download a free, fully functional evaluation copy of Fastvue TMG Reporter v2.1 today. You’ll be glad you did, trust me!
Identifying and Reducing Anonymous Traffic Allowed by Forefront TMG 2010
My recent blog post about altering the SafeSearch enforcement rule in Forefront TMG 2010 to require authentication has sparked some discussion on Twitter and Facebook regarding unauthenticated, anonymous access, particularly to resources located on the public Internet. In a perfect world (ok, my perfect world!), all access to and through the TMG firewall would be fully authenticated. Unfortunately, for a variety of reasons, this isn’t achievable. To start, authenticating all traffic to and through the TMG firewall would necessitate that all clients be configured as explicit web proxy clients. In addition, if non web-based protocols are allowed by firewall policy the Firewall Client would need to be distributed to all clients. While this is ideal if we’re designing a solution on paper, in the real world many administrators don’t have the luxury of forcing proxy configuration or installing the Firewall Client on all their systems. For example, some systems may not be under the administrator’s control or they may be required to support non web-based protocols on platforms other than Windows, for which the Firewall Client is not supported. Also, as veteran ISA and TMG firewall administrators know all too well, there are some applications that simply don’t play nice with an authenticating proxy, even with the Firewall Client installed. Applications that don’t leverage Winsock for network communication or that use IP-based protocols such as ICMP or GRE also prevent us from realizing our goal of authenticating all network traffic through TMG. Windows Update traffic also poses challenges for authenticating all TMG traffic, as the Windows Update service often makes requests to the Internet for updates in the background and perhaps even if there is no interactive user logged on.
Just because out of necessity some traffic has to be allowed through the TMG firewall anonymously doesn’t mean that undertaking an effort to reduce unauthenticated traffic isn’t a worthwhile project. If you’re interested in doing something like this, have a look at the Fastvue blog and read Scott Glew’s excellent article detailing how to use TMG Reporter to identify and reduce unauthenticated traffic on the Forefront TMG 2010 firewall. Not using TMG Reporter? You’re missing out! Download a free evaluation here!
Enable Authentication for SafeSearch Enforcement Rule in Forefront TMG 2010
SafeSearch enforcement in Forefront TMG 2010 is a simple and effective way to prevent users on your network from accessing explicit adult content via popular search engines. Enabling SafeSearch enforcement is accomplished by opening the Forefront TMG 2010 management console, highlighting the Web Access Policy node in the navigation tree, clicking the Configure SafeSearch link in the Tasks pane and selecting the option to Enable SafeSearch.
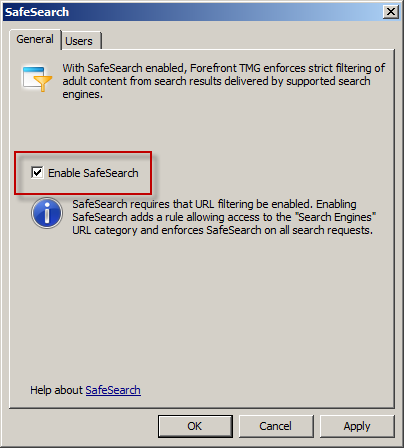
When SafeSearch is enabled a rule is created that grants access to all users from the Internal network to all sites in the Search Engines category.
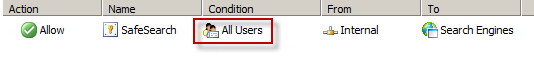
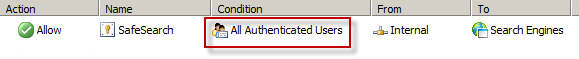
Effectively this grants unauthenticated access to many search engines including Bing, Google, and Yahoo. This level of access is quite broad and enables anonymous users to access quite a bit of content, which might not be desirable in some environments. It is not possible to change the users in the GUI either, unfortunately. However, it can be changed programmatically using COM and VBscript. For example, the following code will change the users from All Users to All Authenticated Users.
Dim Root, Array, Rule
Set Root = CreateObject("FPC.Root")
Set Array = Root.GetContainingArray()
Set Rule = Array.ArrayPolicy.PolicyRules("SafeSearch")
Rule.AccessProperties.UserSets.Add "All Authenticated Users", fpcInclude
Rule.AccessProperties.UserSets.RemoveSpecified "All Users"
Array.Save
Array.WaitForReload
Important Note: This change is not officially supported by Microsoft. If you make this change it may potentially cause other issues, so please proceed with caution.
Once the script has completed the SafeSearch rule will now apply to All Authenticated Users and prevent unwanted anonymous access to web sites categorized as Search Engines.
Hotfix Rollup 3 for Forefront TMG 2010 SP2 Now Available
Hotfix rollup 3 for Microsoft Forefront TMG 2010 with Service Pack 2 is now available for download. This latest hotfix rollup includes fixes for the following issues:
KB2700248 – A server that is running Forefront TMG 2010 may stop accepting all new connections and may become unresponsive
KB2761736 – All servers in a load balanced web farm may become unavailable in Forefront TMG 2010
KB2761895 – The Firewall service (wspsrv.exe) may crash when the firewall policy rules are reevaluated in Forefront TMG 2010
KB2780562 – PPTP connections through Forefront TMG 2010 may be unsuccessful when internal clients try to access a VPN server on the external network
KB2780594 – A non-web-proxy client in a Forefront TMG 2010 environment cannot open certain load-balanced websites when TMG HTTPS inspection is enabled
KB2783332 – You cannot log on when FQDN is used and authentication delegation is set to “Kerberos constrained delegation” in a Forefront TMG 2010 environment
KB2783339 – A closed connection to a domain controller is never reestablished when authentication delegation is set to “Kerberos constrained delegation” in a Forefront TMG 2010 environment
KB2783345 – Unexpected authentication prompts while you use an OWA website that is published by using Forefront TMG 2010 when RSA authentication and FBA are used
KB2785800 – A “DRIVER_IRQL_NOT_LESS_OR_EQUAL stop error may occur on a server that is running Forefront TMG 2010
KB2790765 – A “Host Not Found (11001)” error message occurs when an SSL site is accessed by using a downstream Forefront TMG 2010 server that has HTTPS Inspection enabled
You can download hotfix rollup 3 for Forefront TMG 2010 SP2 here. After applying this update, the new Forefront TMG 2010 build number will be 7.0.9193.575.
PAL v2.3.3 Now with Forefront UAG 2010 Support
Recently the Performance Analysis of Logs (PAL) tool was updated and now includes a threshold file for Forefront UAG 2010. PAL is an essential utility that can make troubleshooting performance issues or capacity planning dramatically easier. I’ve written about using PAL on Forefront TMG 2010 in the past, and using PAL with Forefront UAG 2010 will be very similar. You can download the latest release of PAL at pal.codeplex.com.
Forefront TMG 2010 Replacement Options
Since Microsoft formally announced the end of life for the venerable Forefront TMG 2010 firewall, the most common question I hear is “What should I replace my Forefront TMG firewall with?” It’s an excellent question, and one that I can’t really answer for you definitively. Since Microsoft has elected to leave this space entirely, you’ll obviously be replacing it with a solution from another vendor. But which one? Well, the answer is “it depends”. There are many excellent firewalls, web proxies, and secure web gateways on the market today. So-called “Next Generation Firewalls” are gaining in popularity as well, and provide some interesting capabilities a security administrator can leverage to provide increased protection for their corporate networks. Which one to choose depends on many factors, and will vary greatly depending on your deployment scenario. My suggestion when evaluating potential replacements for your Forefront TMG 2010 firewall is to take a look at your current configuration, review your corporate security policy to determine network security requirements, then begin researching products that include the features you need. If you take a look at the latest Gartner Magic Quadrant for Secure Web Gateways or Next Generation Firewalls and choose a product in the leaders or challengers quadrants you will probably be satisfied. Regardless which solution you choose, demand a proof-of-concept or insist on an evaluation period with which you can return the product for a full refund if it doesn’t meet your needs or expectations. Be open-minded during the process, as you’re not likely to have the comfort level with the new solution as you do with your existing Forefront TMG 2010 firewall. If you are using your Forefront TMG 2010 firewall as a dedicated remote access solution, I would encourage you to look closely at Windows Server 2012 remote access VPN and especially DirectAccess.
Keep in mind that although Microsoft has announced the end of life for Forefront TMG 2010, it will still be supported for many years to come. You will have full feature functionality until the end of 2015, and the product will be supported in some fashion until early 2020 so there’s no need to rush. Perhaps the best replacement for Forefront TMG 2010 hasn’t even been created yet! If you have questions about Forefront TMG 2010 replacements, or you are in the process of evaluating another solution to replace your existing Forefront TMG firewall today, feel free to ask questions or share your experiences by commenting below. Thanks!
Forefront TMG 2010 Configuration Change Tracking Description Quick Tip
Configuration change tracking is an important tool that can be leveraged by Forefront TMG 2010 firewall administrators to audit changes made to the policy and configuration of TMG. This feature originally appeared with ISA 2006 SP1 and was optionally enabled by the administrator. Beginning with Forefront TMG 2010 this feature is now enabled by default. When applying changes made to TMG, the administrator is prompted to enter a description of the change which is included in the change tracking log.
![]()
If you check the box Do not show this prompt again you will, of course, not be prompted to enter descriptions for applied changes in the future. If you later decide you’d like to have this feature back, highlight the Troubleshooting node in the navigation tree and select the Change Tracking tab in the main window. In the Tasks pane click Configure Change Tracking and check the box next to Show prompt for a change description when applying configuration changes.
![]()
Windows 8 Modern UI Apps and Forefront TMG 2010
On a Windows 8 client deployed behind a Forefront TMG 2010 firewall, users may receive the following error when trying to open the Windows Store app.
You’re PC isn’t connected to the Internet. To use the Store, connect to the Internet and then try again.
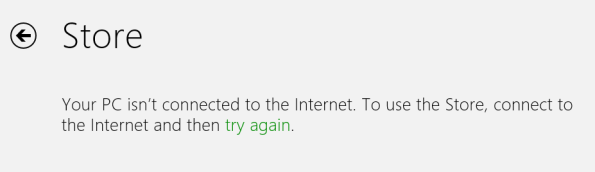
Other Windows 8 “modern UI” applications may experience similar behavior if they require access to resources on the public Internet. However, you are able to access the Internet using both the modern UI and desktop versions of Internet Explorer 10.
The problem occurs when the Forefront TMG 2010 firewall is configured to require authentication on rules controlling access to the Internet over HTTP and HTTPS, or if the option to require all users to authenticate is enabled on the web proxy listener (which isn’t a good idea!). Authenticated web proxy access requires that client be configured either as a web proxy client or as a firewall client. Internet Explorer can be configured as a web proxy client, typically using automatic configuration (WPAD) through DNS or DHCP, but Windows 8 modern UI applications do not inherit Internet Explorer proxy server settings. As such, they behave as SecureNAT clients which do not support authentication. To resolve this issue, run the following command from an elevated command prompt on the Windows 8 client.
netsh winhttp set proxy <tmg_hostname_or_IP_address>:<web_proxy_listener_port>
For example…
netsh winhttp set proxy tmg.richardhicks.net:8080
More information about configuring WINHTTP can be found here.
Another workaround is to install the Forefront TMG 2010 firewall client. This will ensure that all outbound communication through the Forefront TMG firewall is always authenticated.
Forefront TMG 2010 End of Life Statement
Note: This post updated on 4/22/2015 to reflect current information about the status of the Microsoft Reputation Service (MRS) after December 1, 2015.
Today, Microsoft announced the Forefront TMG 2010 product will be discontinued. Microsoft will continue to provide mainstream support for TMG until April 14, 2015, and extended support until April 14, 2020. The Forefront TMG 2010 Web Protection Services (WPS) will be discontinued on December 31, 2015. Beginning on January 1, 2016, Web Protection Service (URL filtering) will cease to function and the Microsoft Reputation Service (MRS) will be shutdown permanently. Virus and malicious software scanning and the Network Inspection System (NIS) will continue to operate but will no longer receive updates.
The end of life for Forefront TMG 2010 comes as part of sweeping changes made to the entire Forefront protection suite of products. In addition to ending development of Forefront TMG 2010, Microsoft also announced that Forefront Protection for Exchange (FPE), Forefront Protection for SharePoint (FPSP), Forefront Security for OCS (FSOCS), and Forefront Protection Server Management Console (FPSMC) are all being discontinued. Forefront Online Protection for Exchange (FOPE), which has been a part of Office 365, is being renamed Exchange Online Protection.
Looking ahead, Forefront Unified Access Gateway (UAG) 2010 and Forefront Identify Manager (FIM) 2010 R2 both have current roadmaps and will continue to be developed, although it is likely that they will not continue under the Forefront brand name.
Forefront TMG 2010 Protocols and Ports Reference
When deploying Forefront TMG 2010 as a forward or reverse proxy, many organizations will place their TMG firewalls in a perimeter or DMZ network to provide an additional layer of protection for their proxies. When deployed in this manner, configuring perimeter firewalls to allow proper communication to and from the Forefront TMG firewall can be challenging. Although the Service Overview and Network Port Requirements for Windows document on TechNet includes information about ISA server (which also applies to TMG) it includes all protocols and ports used by TMG in all deployment scenarios. This can be confusing when you simply want to allow TMG firewalls in a perimeter network to communicate with an Enterprise Management Server (EMS) on the internal network, or simply manage a TMG firewall in a perimeter network from a management workstation on the internal network. Opening all of the ports listed in the Microsoft KB article mentioned above would be unnecessary and would violate the principle of least privilege, which dictates that only the specific ports required for communication should be opened.
Note: This reference covers typical TMG configurations and may not include all protocols and ports required for every deployment scenario. For example, if you are using RADIUS or RSA for authentication, have configured connectivity verifiers or a remote SQL server, or have deployed Forefront TMG 2010 for Exchange integration, each of these configurations will require additional perimeter firewall access. Also, don’t forget that your perimeter firewalls will need to allow access to the protocols and ports required for the services you are accessing/publishing through Forefront TMG 2010.
For reference, here are the protocols and ports required for specific, common Forefront TMG 2010 deployment scenarios:
EMS to TMG
TCP 135, 10000-65535* – RPC
TCP 3847 – MS Firewall Control
TMG to EMS
TCP 445 – CIFS
UDP 445 – CIFS
TCP 2171 – MS Firewall Storage (domain-joined only)
TCP 2172 – MS Firewall Storage Secure (workgroup mode only)
TCP 3847 – MS Firewall Control
TMG to DCs
Domain joined…
TCP 88 – Kerberos
UDP 88 – Kerberos (send receive)
UDP 123 – NTP
TCP 135, 49152-65535* – RPC
TCP 389 – LDAP
UDP 389 – LDAP
TCP 445 – CIFS
UDP 445 – CIFS
TCP 3268 – LDAP Global Catalog
Non domain-joined…
TCP 389 – LDAP (required only for pre-authentication in reverse proxy scenarios)
TCP 636 – LDAPS (required only for pre-authentication in reverse proxy scenarios)
TMG to DNS
TCP 53 – DNS (send receive)
UDP 53 – DNS
Primary EMS to Replica EMS
TCP 135, 49152-65535* – RPC
TCP 2173 – MS Firewall Storage Replication
Replica EMS to Primary EMS
TCP 135, 49152-65535* – RPC
TCP 445 – CIFS
UDP 445 – CIFS
TCP 2171 – MS Firewall Storage – domain-joined only
TCP 2172 – MS Firewall Storage (Secure) – workgroup mode only
TCP 3847 – MS Firewall Control
Web Proxy Client to TMG
TCP 80 – HTTP (WPAD only)
TCP 8080 – HTTP Proxy
Firewall Client to TMG
TCP 80 – HTTP (WPAD only)
TCP 1745 – Firewall Client Control Channel
UDP 1745 – Firewall Client Control Channel
TCP 1024-65535 – All high ports**
UDP 1024-65535 – All high ports**
Management Workstation to TMG
TCP 135, 10000-65535* – RPC
TCP 2171 – MS Firewall Storage – Domain mode only
TCP 2172 – MS Firewall Storage (Secure) – Workgroup mode only
TCP 3847 – MS Firewall Control
*The default dynamic port range for Windows Server 2008 R2 is 49152-65535. When TMG is installed this setting is changed to 10000-65535. This does not apply to TMG EMS, however. RPC can be configured to use a smaller range of dynamic ports, if necessary. For more information, please see Microsoft KB 154956.
**The Forefront TMG 2010 Firewall Client is designed to operate without a firewall between itself and the TMG firewall. It is highly recommended that you avoid this design whenever possible. If this is unavoidable, all TCP and UDP high ports will have to be opened, as the TMG Firewall Client control channel utilizes random high ports and cannot be restricted as RPC can.





