Archive
IP Spoofing Alert from APIPA Address in Forefront TMG 2010
Security administrators may encounter the following IP spoofing alert on their Forefront TMG 2010 firewall:
Alert: IP Spoofing Description: Forefront TMG 2010 detected a possible spoof attack from the IP address 169.254.x.x. A spoof attack occurs when an IP address that is not reachable through the network adapter on which the packet was received. If logging for dropped packets is enabled, you can view the details of this attack in the firewall log in Forefront TMG 2010 log viewer. If the IP address belongs to a VPN client, this event may be ignored.

This alert occurs because the Forefront TMG 2010 firewall received a packet on its internal network interface from a client (server, workstation, or other host) that did not have a statically assigned IP address and was not able to obtain one from DHCP, so the client selected an IP address from the Automatic Private IP Address Assignment (APIPA) address range defined in RFC 3927.
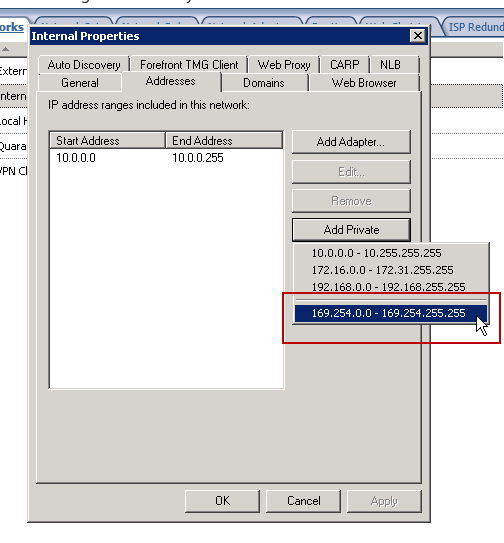
You can safely ignore this alert, or you can resolve the issue by adding the APIPA reserved network 169.254.0.0/16 to the Internal network definition. This can be accomplished by opening the Forefront TMG 2010 management console and highlighting the Networking node in the navigation tree, then right-clicking the Internal network, selecting the Addresses tab, then clicking the Add Private button and choosing the address range 169.254.0.0 – 169.254.255.255.
Note: It is possible to resolve this issue by disabling alerts for IP spoofing attempts. However, this is considered bad security practice and is strongly discouraged.
You may recall from an earlier blog post I indicated that the best way to configure the Internal network definition in Forefront TMG 2010 is to choose the Add Adapter option. This still remains true. However, this is one of those rare cases in which you’ll want add an additional network address space to your Internal network definition to reduce the volume of IP spoofing alerts being raised by the Forefront TMG 2010 firewall.
The one side effect to implementing this change is that you will now receive a Configuration error alert informing you that your Internal network does not correlate with the network adapters that belong to it.
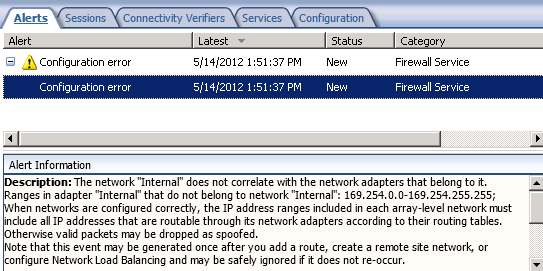
Essentially you have traded one annoying alert for another. However, the noise generated by IP spoofing alerts from clients with APIPA IP addresses might make this tradeoff worthwhile. In addition, it is much safer to disable the configuration error alert than it is the IP spoofing alert.
Hotfix Rollup 2 for Forefront TMG 2010 SP2 Now Available
The latest hotfix rollup for Forefront TMG 2010 SP2 is now available. This update includes fixes for the following issues:
KB2701952 – “Access is denied” status error when you use a delegated user account to try to monitor services in Forefront TMG 2010.
KB2700248 – A server that is running Forefront TMG 2010 may randomly stop processing incoming traffic.
KB2700806 – Connectivity verifier that uses the “HTTP request” connection method may not detect when a web server comes back online in Forefront TMG 2010.
KB2705787 – The Firewall service may intermittently crash when it processes client web proxy requests in a Forefront TMG 2010 environment.
KB2701943 – Error message when you try to join a Forefront 2010 server to an array: “The Operation Failed. Error code – 0x80070002 – the system cannot find the file specified”.
KB2705829 – The Firewall service may stop responding to all traffic on a server that is running Forefront TMG 2010.
KB2694478 – Dynamic Caching may incorrectly delete recently cached objects from a caching server that is running Forefront TMG 2010 or ISA Server 2006.
You can download hotfix rollup 2 for Forefront TMG 2010 SP2 here. After applying this update, the new Forefront TMG 2010 build number will be 7.0.9193.540.
Presenting Forefront TMG and UAG 2010 at TechEd 2012
I’m excited to announce that I will be presenting a session at both TechEd North America and TechEd Europe this year! The session I will be delivering is entitled Demystifying Forefront Edge Security Technologies: TMG and UAG. During this level 200 session I’ll provide an overview of both Forefront TMG 2010 and UAG, describing their high level function and operation. I will also outline common deployment scenarios for each product and highlight the similarities and differences between the two. The session will also include demonstrations of Forefront TMG 2010’s advanced web protection capabilities, Forefront UAG 2010’s application publishing features, and an introduction and demonstration of Forefront UAG and DirectAccess. TechEd North America takes place in Orlando, Florida on June 11-14, 2012. TechEd Europe will be held in Amsterdam June 26-29, 2012. Looking forward to seeing you there!
TechDays San Francisco 2012
TechDays San Francisco 2012, sponsored by the Pacific IT Professionals user group, is a two day IT professional conference being held on March 23 and 24, 2012. The event features a lineup of speakers that includes Chris Avis, CA Callahan, Jennelle Crothers, Jessica DeVita, Steve Evans, Jason C. Helmick, Chris Henley, Ed Horley, Darren Mar-Elia, Mark Minasi, Stephen Rose, Joey Snow, Doug Spindler, Mark Vinkour, Harold Wong, and Chris Zwergel. Sessions will cover topics such as Azure and cloud, Clustering, DNS/DHCP/IPAM, Exchange, Hyper-V, IIS, Lync, MDOP, networking and VPN, Powershell, SharePoint, System Center, VDI, Windows 8 Client and Server, and Windows Phone 7. I will be presenting sessions on Forefront Edge Security (Forefront TMG 2010 and UAG 2010) as well as DirectAccess. Visit the TechDaysSF web site for the full speaker lineup and session abstracts, then click here to register for the event. Hope to see you there!
Fastvue Enhanced Reporting for Forefront TMG 2010
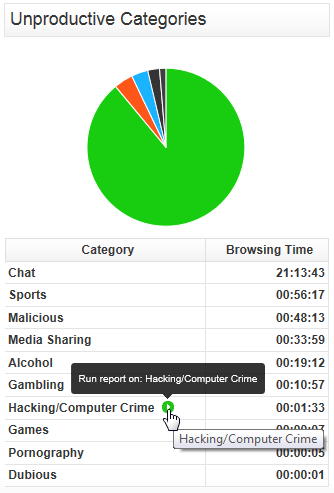
Recently I had the pleasure of reviewing the Fastvue Dashboard product for Forefront TMG 2010 at ISAserver.org. Fastvue is a real-time dashboard that integrates with Forefront TMG to provide a nearly instantaneous view of traffic being controlled by your TMG firewall. Although the real-time dashboard is a nice feature, if you’ve spent any time at all with Forefront TMG 2010’s native reporting tools you know that TMG is severely lacking in this area. A major limitation of Forefront TMG 2010’s in-box reporting is that the reports are generated using summarized data. Data summarization occurs only once daily, so reports can be lacking essential information if you are looking for recent activity. In addition, the native reports are static and one-dimensional. If a report reveals something interesting that you want to know more about, creating and generating a new report is required.
Thankfully the good folks at Fastvue recognized these shortcomings and have addressed many of these issues with their latest release. Fastvue v2.0 now includes full historical reporting capabilities, with detailed company overview and user investigation reports that can be shared via e-mail. Reports can also be scheduled to run automatically. The reports are highly interactive, allowing the administrator to dynamically drill down to generate more granular reports in an instant.
The current version of Fastvue is priced at $395.00 per TMG firewall. The newest version will be priced at $795.00 per server. However, for a limited time, readers of my blog can purchase Fastvue v1.0 for the current price and receive a free upgrade to v2.0 when it is released. Click here to download a trial of the software and to take advantage of this offer!
WPAD Considerations for Kerberos Authentication with NLB VIP on Forefront TMG 2010
As I outlined in a recent article on ISAserver.org, Service Pack 2 (SP2) for Forefront TMG 2010 supports Kerberos authentication in load-balanced scenarios when web proxy clients are configured to use the virtual IP address (VIP) of the array. However, using Web Proxy Automatic Discovery (WPAD) with either DNS or DHCP poses a challenge for organizations that choose to take advantage of this new feature. When using WPAD, the web proxy client retrieves the automatic configuration script from the Forefront TMG firewall. The script provides the web proxy client with the IP addresses (or hostnames, if configured) of the individual array members. In this configuration, the web proxy client will send its request to one of the array members returned by function MakeProxies() and not to the VIP, as desired.
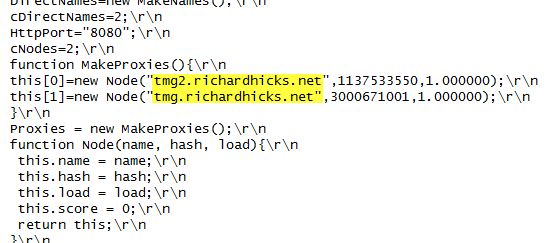
To work around this issue you can configure a separate web server to host the automatic configuration script. You can use any web server you wish, just make sure that it is highly available and don’t forget to configure the MIME type application/x-ns-proxy-autoconfig for the file extension you choose (typically .DAT or .PAC). Full details about how to do this can be found here. You can create your own Proxy Automatic Configuration (PAC) file from scratch, or you can simply retrieve the automatic configuration script from TMG, modify it to use the IP address (or preferably the hostname or FQDN) of the Forefront TMG array’s VIP, and place that on the web server for clients to retrieve. This means that the automatic configuration script will have to be updated manually, as required. This could be automated by writing a script that periodically retrieves the automatic configuration script from the Forefront TMG firewall, modifies it appropriately, and then saves it on the web server if you were really clever! Another alternative is to configure the Forefront TMG 2010 firewall to return a customized automatic configuration script. You can find details about this configuration here.
ESET Gateway Security Beta for Forefront TMG 2010
For security administrators looking to improve upon Forefront TMG 2010’s already strong advanced web protection features, leading anti-virus vendor ESET recently announced the beta availability of its Gateway Security for Forefront TMG 2010 software. ESET Gateway Security for Forefront TMG delivers advanced, gateway-integrated virus and malicious software scanning to provide comprehensive protection for web-based protocols like HTTP and FTP. ESET Gateway Security for Forefront TMG also supports SMTP, IMAP, and POP3 protocols to provide anti-malware and anti-spam capabilities for added protection. In addition, ESET Gateway Security for Forefront TMG 2010 includes host-based security for the TMG firewall’s underlying operating system, as well as automatic file exclusion configuration to ensure compatibility with Forefront TMG. ESET Gateway Security for Forefront TMG 2010 is fully compatible with existing ESET centralized management tools and supports Microsoft ISA Server 2006. Download the beta today!
Configuring SQL Memory Limits on Forefront TMG 2010
When Forefront TMG 2010 is installed, an instance of SQL Server 2008 Express is also installed to facilitate local firewall and web proxy logging. Some TMG administrators have reported that the SQL server process (sqlservr.exe) may consume an excessive amount of memory.
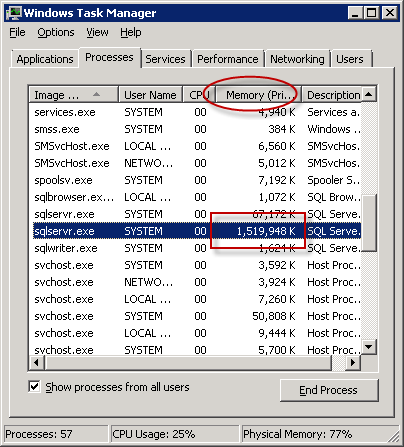
This occurs because SQL server performs its own internal memory management. By design it will consume large amounts of memory and hold it in reserve, which may appear to be a memory leak. However, if you observe the memory consumed by SQL server over an extended period of time, you will notice that it will periodically release memory as well.
In most cases, allowing SQL to handle the job of managing its memory without restriction poses no real problem. However, if your system is exhibiting signs of high memory pressure and you are confident that there are no other processes that are consuming excessive amounts of memory, you can configure SQL to limit the amount of memory that it will reserve. Before manually configuring SQL memory limits, review this blog post for a list of recommended settings.
Next, open an elevated command prompt and enter the following command:
osql –E –S .\msfw
After connecting to the SQL instance, enter the following commands:
USE master GO EXEC sp_configure 'show advanced options', 1 RECONFIGURE WITH OVERRIDE GO EXEC sp_configure 'max server memory (MB)', 1024 --configure 1GB limit, adjust as needed GO EXEC sp_configure 'show advanced options', 0 RECONFIGURE WITH OVERRIDE GO
This script assumes that you’ve chosen a 1GB (1024MB) memory limit. You can adjust the script above to reflect the values for your environment as required. Once complete, restart the SQL server service for the changes to take effect.
To view the currently configured memory limit, simply omit the numeric value after max server memory (MB), as shown here:
EXEC sp_configure 'max server memory (MB)'
To make things easier you can download these as script files and execute them using the following command:
osql –E –S .\msfw -i <path to script file>
You can find script files to show and set SQL memory limits here:
Hotfix Rollup 1 for Forefront TM 2010 SP2 Now Available
A hotfix rollup for Forefront TMG 2010 SP2 is now available. The hotfix rollup resolves several reported issues with TMG, including:
KB2654016 – A client may be unsuccessful in accessing a Java SSO application published to the web by Forefront TMG 2010
KB2653703 – “Error: Subreport could not be shown” error message in the User Activity or Site Activity report in Forefront TMG 2010
KB2654585 – UDP packets may become backlogged when you increase the “maximum concurrent UDP sessions per IP address” setting in Forefront TMG 2010
KB2624178 – Forefront TMG 2010 administrators may be unable to generate reports
KB2636183 – Both sides of a TCP connection are closed when the client or remote application half-closes the TCP connection in Forefront TMG 2010
KB2653669 – Summary information for the Top Overridden URLs table and for the Top Rule Override Users table display incorrect information in Forefront TMG 2010
KB2617060 – Forefront TMG 2010 enables L2TP site-to-site connections in RRAS
KB2655951 – Japanese characters in the subject line of an Alert email message are not readable in the Japanese version of Forefront TMG 2010
KB2654068 – “The Web Listener is not configured to use SSL” warning message may occur when you configure a Web Listener to use a valid SSL certificate in Forefront TMG 2010
KB2654193 – You receive a “Bad Request” error message when you try to access Outlook Web App published by Forefront TMG 2010
KB2654074 – String comparison may become case-sensitive when you published a website using Forefront TMG 2010
KB2658903 – Forefront TMG 2010 firewall service (wspsrv.exe) may crash frequently for a published website secured by SSL after you install Service Pack 2.
Hotfix rollup 1 for Forefront TMG 2010 SP2 can be downloaded here. After applying this update, the new Forefront TMG 2010 build number will be 7.0.9193.515.












